CALL CENTER COMPLIANCE
Call Center Compliance for Nearshore BPOs in 2026: A Practical Guide for Regulated Teams
Learn how to build a resilient call center compliance program for a bilingual nearshore BPO with practical guidance on TCPA, data handling, monitoring, audits, and cross-border risk control.
TL;DR — Quick Takeaways
- Call center compliance is operational, not theoretical. Policies only matter when agents can follow them correctly on live calls and managers can prove it.
- Regulated teams must design for proof. Scripts, consent controls, CRM logic, monitoring, and access permissions all need to work together.
- Bilingual nearshore support adds both opportunity and risk. English and Spanish workflows require separate validation, not simple translation.
- Strong compliance programs improve quality. Better controls reduce avoidable errors, customer friction, repeat contacts, and preventable exposure.
Meta title: Call Center Compliance for Nearshore BPOs in 2026 | Practical Guide for Regulated Teams
Meta description: Learn how to build a resilient call center compliance program for a bilingual nearshore BPO. Practical guidance on TCPA, data handling, monitoring, audits, and cross-border risk control.
Is your customer support operation helping you grow, or creating legal and operational risk?
Many companies still treat call center compliance like a legal checklist. That approach fails fast in real operations. The issue is not whether a policy exists in a folder. It is whether agents follow the right process on live calls, whether managers can prove it, and whether your partner can handle those standards across languages, teams, and borders.
For healthcare, finance, e-commerce, insurance, and telecom, that difference matters. A weak process can create liability through outbound calling, payment handling, disclosure failures, or poor data controls. A strong process does the opposite. It protects customer trust, keeps campaigns moving, and gives leadership confidence that growth will not trigger preventable problems.
Compliance isn’t a department. It is the operating system behind trust, scale, and defensible service quality.
If your organization is also reviewing shifting U.S. policy expectations around domestic and nearshore support models, the Keep Call Centers in America Act of 2025 is part of the broader context worth watching.
Introduction Is Your Call Center a Compliance Time Bomb
A call center becomes risky long before a regulator gets involved.
It happens when agents improvise disclosures. When marketing hands over lead lists without clean consent records. When a bilingual team uses one script in English and a rough translation in Spanish. When supervisors listen to a few calls each week and assume that is enough oversight.
That is how companies end up surprised by problems that were visible in plain sight.
Why call center compliance matters in day-to-day operations
The most common mistake is treating compliance as something separate from performance. In live operations, it is tightly connected to quality.
A weak process creates repeat contacts, escalations, customer distrust, and inconsistent documentation. A strong process makes work cleaner. Agents know what to say, what not to say, how to authenticate the caller, when to escalate, and how to handle sensitive information without guessing.
For nearshore programs, the stakes rise further. Teams often support U.S. customers while operating from Mexico, serving both English and Spanish speakers. That setup creates practical advantages, but it also adds complexity that many generic compliance guides never address.
What resilient programs do differently
The strongest compliance environments share a few traits:
- They design for proof. It is not enough to tell agents to follow policy. Managers need records, call monitoring, permissions, and documented workflows.
- They reduce judgment calls. Good systems remove unnecessary improvisation through approved scripts, prompts, and CRM controls.
- They coach in real time. Problems get corrected during operations, not weeks later in a spreadsheet review.
- They account for language and jurisdiction. A bilingual nearshore operation needs governance that reflects real customer interactions, not a U.S.-only template.
A compliance program should feel practical on the floor. If it only sounds good in audit language, it will break under production pressure.
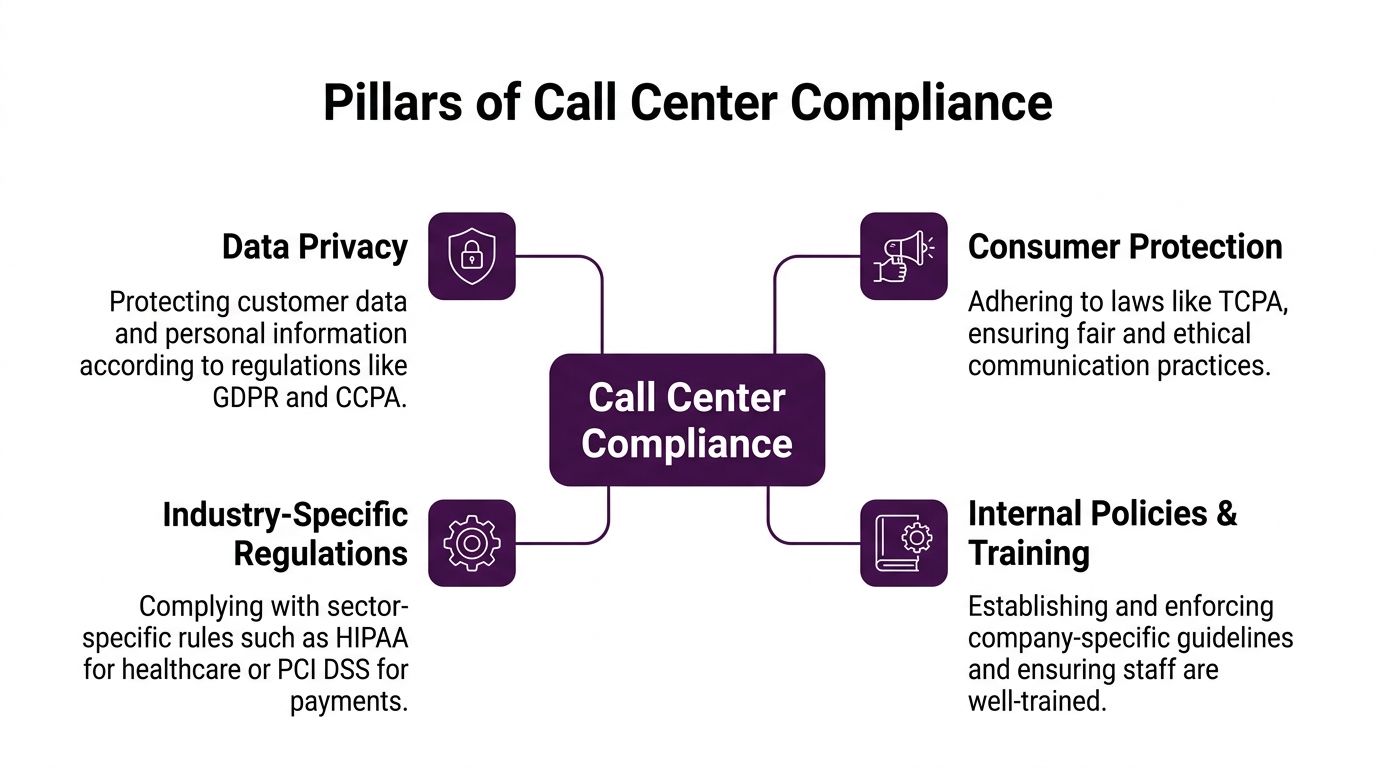
Understanding the Pillars of Call Center Compliance
Think of compliance like maintaining a high-performance vehicle. Brakes, steering, engine, and electronics all need different checks. A call center works the same way. Calling rules, data privacy, payment security, and internal governance each solve a different risk.
If you want a practical view of how these requirements intersect with outsourcing in Mexico, this overview of security compliance in MX BPOs is useful context.
Consumer protection rules
For outbound programs, TCPA is one of the first places leadership should look.
The operational point is simple. If your team uses autodialed or prerecorded calls to cell phones, prior express written consent is required, and violations can result in $500 to $1,500 per call. Non-compliance also creates class-action risk, and even a single unconsented call to 1,000 customers can exceed $500,000 in liability according to Giva’s call center compliance guidance.
That is why smart outbound teams do not rely on verbal assurances from sales or marketing. They verify consent status in the CRM, maintain suppression logic, and document when and how consent was captured.
Data privacy rules
Privacy laws shape how you collect, store, access, and delete customer information.
In practical terms, these rules affect:
- What agents can see: Limit access to the minimum data needed to complete the task.
- What teams can say aloud: Agents should not read unnecessary personal information back to a customer.
- How systems store records: Notes, recordings, and attachments need retention and access controls.
- How requests are handled: Consumer requests related to personal data need a documented workflow.
Privacy obligations matter even more when work crosses borders. Once customer data moves between systems, vendors, and locations, loose process design becomes dangerous.
Industry-specific requirements
Some regulations depend on what your business handles, not just that you operate a contact center.
A healthcare support line has different exposure than a retail order line. A payment-heavy queue has different controls than a scheduling desk. In operations, that means script design, screen access, recording settings, and escalation paths cannot be identical across every line of business.
A few examples make this clear:
| Operational scenario | Primary compliance concern | What changes on the floor |
|---|---|---|
| Outbound sales campaign | Consent and disclosures | Approved scripts, DNC controls, documented opt-outs |
| Healthcare appointment support | Sensitive health information | Tighter authentication, restricted notes, controlled escalation |
| Payment by phone | Cardholder data handling | Secure capture process, recording controls, limited exposure |
Internal policies and training
Many failures start inside the operation, not in the law itself.
Policies translate legal requirements into behaviors. Training turns those behaviors into habits. QA confirms whether those habits survive under call pressure.
A rule only becomes operational when an agent can follow it correctly during a difficult conversation, with the clock running and the customer waiting.
The best internal policies are short, specific, and tied to workflow. “Protect customer data” is too vague. “Do not repeat full payment details aloud, and use the approved payment capture path” is actionable.
Building your Ironclad Compliance Framework
A resilient program rests on three things: people, policies, and technology. If one is weak, the others carry too much weight.
The reason this framework matters is simple. The penalties attached to failures are not abstract. TSR violations can carry penalties up to $43,792 per incident, while the FTC Safeguards Rule imposes fines up to $100,000 per violation, as outlined by AmplifAI’s call center compliance analysis.
 Start with policies agents can use
Start with policies agents can use
A policy manual should not read like a legal memo.
Frontline teams need a playbook built around real interactions. That includes:
- Required disclosures: Exact language for outbound calls, opt-outs, identity statements, and sensitive conversations.
- Authentication steps: What must be verified before discussing account details.
- Data handling rules: What can be entered into notes, what cannot be stored, and where sensitive details belong.
- Escalation triggers: When an agent must pause, transfer, or involve a supervisor or compliance lead.
A healthcare script and a retail script should not look the same. In healthcare, identity verification and the handling of sensitive information need tighter control. In retail, the emphasis may shift toward payment handling and order updates. The structure changes because the risk changes.
Build controls into systems
Policies fail when systems make the wrong action easy.
A few controls consistently work well in nearshore operations:
CRM-based consent and disposition controls
Outbound teams should not depend on memory for consent checks. The CRM should display status clearly and require proper dispositions when a customer opts out, disputes consent, or requests no further contact.
That control matters because it turns a legal requirement into a step the agent cannot skip.
Secure recording and redaction workflows
Recording is useful for QA and dispute handling, but it can also create risk if sensitive information is captured unnecessarily. Strong environments use recording controls, pause logic where appropriate, and restricted playback permissions.
Role-based access
Not every agent needs the same view. Segment access by queue, function, and client need. If an agent only handles scheduling, they should not see broad account history or extra financial detail.
For organizations evaluating stack design, CallZent’s technology approach shows how compliance controls and operational tools need to work together rather than sit in separate silos.
Train for live-call pressure
Most training programs are too theoretical.
Agents do not struggle with compliance because they forgot a definition. They struggle because customers interrupt, ask for exceptions, switch languages mid-call, or pressure them to move faster.
The better approach is scenario-based training:
- Disclosure drills: Practice opening statements until agents can deliver them naturally, not mechanically.
- Objection handling within policy: Teach agents how to keep the conversation moving without changing approved language.
- Language consistency: For bilingual teams, validate not just translation, but intent and legal meaning.
- Escalation reps: Make it normal to pause and escalate when a situation falls outside policy.
If agents only hear compliance in onboarding, managers should expect failure during production.
Assign ownership clearly
Frameworks weaken when everyone assumes someone else owns the issue.
A practical model usually includes:
- Operations managers who own adherence on the floor
- QA leaders who monitor and score behavior
- IT or security teams who manage system controls
- Client stakeholders who approve scripts and required workflows
- Compliance leads who resolve gray areas and document change
One provider option in this space is CallZent, which offers bilingual nearshore support and back-office operations. In practice, what matters is whether any provider can align scripts, controls, training, and reporting with the client’s regulatory exposure.
Monitoring Auditing and Continuous Improvement
A policy without verification is just optimism.
Older contact centers often relied on random call reviews. That model misses too much. It might catch obvious script drift, but it rarely gives leaders a reliable view of what is happening across an entire program.

For teams trying to move from anecdotal oversight to measurable control, this guide on monitoring call center performance connects QA discipline with operational visibility.
What to monitor in a compliance-driven operation
Monitoring should answer four questions:
- Did the agent follow the required process?
- Did the system support the right behavior?
- Did the customer interaction create any new risk?
- Did the issue get resolved cleanly enough to avoid repeat exposure?
That last point is often overlooked.
Top-performing compliant call centers maintain a First Call Resolution rate between 75% and 85%, and high FCR reduces repeat contacts and data exposure risk while cutting non-compliance flags by up to 40%, according to KYP.ai’s call center metrics guide.
Why FCR belongs in compliance reviews
Many leaders still treat FCR as a pure service metric. In regulated environments, it is also a risk metric.
Every unnecessary repeat contact creates another chance for:
- failed authentication
- missing disclosures
- inconsistent documentation
- avoidable frustration that escalates into complaints
A program with poor resolution quality usually creates compliance noise somewhere else. Rework and risk tend to travel together.
Replace spot checks with broader visibility
Modern QA programs use technology to review interactions at scale. That helps supervisors find patterns that random sampling would miss, such as:
- recurring script deviations on one campaign
- inconsistent opt-out handling by one team
- a bilingual phrasing issue that only appears in Spanish calls
- agents skipping a required identity step during busy hours
That wider visibility matters because risk rarely appears as a single dramatic event. More often, it shows up as a repeated small failure spread across many calls.
Audit trends, not just incidents. A single bad call needs coaching. A repeated pattern needs process redesign.
Turn findings into a closed loop
Monitoring alone does not improve compliance. Teams need a review cycle that changes behavior.
A practical loop looks like this:
| Step | What happens |
|---|---|
| Review | QA and managers examine flagged calls, notes, and workflow records |
| Diagnose | They determine whether the issue came from training, scripting, systems, or staffing pressure |
| Correct | Coaching, script updates, permission changes, or workflow fixes are implemented |
| Confirm | The team checks whether the same issue appears again in later interactions |
The best programs also include periodic internal audits and outside validation. Not because leaders expect failure, but because blind spots are normal in live operations.
The Nearshore Advantage in Bilingual Call Center Compliance
Nearshore compliance gets oversimplified in both directions.
Some buyers assume a cross-border setup is automatically risky. Others assume bilingual service is just a staffing feature. Both views miss the operational reality. A bilingual nearshore program can be a compliance strength, but only when it is designed as one.
Most compliance guides ignore the hard part. They do not explain how consent disclosures, required scripts, and identification rules must be adapted for Spanish-language interactions, or how to manage data residency rules across the U.S.-Mexico border, a gap highlighted in Global Response’s discussion of call center compliance.
If you are evaluating a provider model rather than just labor arbitrage, nearshore outsourcing management services is the right lens.
Where bilingual operations get exposed
The trouble usually starts with translation.
A script that is compliant in English can become risky when translated too closely, shortened by agents, or adapted informally to sound more natural. That affects disclosures, consent language, identity statements, and escalation instructions.
A few examples show the difference between a mature operation and a fragile one:
- Weak practice: One English script, loosely translated by supervisors, with no legal or QA review.
- Stronger practice: Separate approved language by interaction type, validated for both meaning and operational clarity.
- Weak practice: QA scorecards that only check for completion.
- Stronger practice: QA scorecards that test whether the disclosure was delivered correctly in the language used on the call.
Why nearshore can improve compliance discipline
A well-run nearshore operation offers practical advantages.
Teams in Tijuana work in close alignment with U.S. time zones. That makes governance easier. Clients can join calibrations, review calls quickly, update scripts faster, and resolve policy questions without waiting through large time-zone gaps.
Bilingual capacity also matters beyond coverage. It reduces the temptation to route Spanish-speaking customers through agents who can “get by.” In compliance-sensitive interactions, partial fluency is not enough. The customer has to understand what is being disclosed, what is being requested, and what happens next.
What strong cross-border governance looks like
The clients that manage this well usually require:
- Approved bilingual scripts for every high-risk interaction type
- Cross-border data mapping that identifies where customer information moves
- Escalation rules for any request that touches privacy, identity disputes, or regulated data handling
- Calibration sessions that include operations, QA, and client-side stakeholders
- Language-aware QA reviews so Spanish interactions are not scored by English-only assumptions
That is where nearshore becomes an asset. Proximity supports tighter oversight. Bilingual staffing supports accurate communication. A structured governance model turns both into compliance resilience.
Your Actionable Call Center Compliance Checklist
If you are reviewing your own operation or vetting a BPO partner, use this as a working checklist. The right questions expose maturity quickly.
For a deeper operational view of privacy controls in outsourced environments, see these best practices for protecting customer privacy in BPO.
 Data handling and system access
Data handling and system access
- Can you map where customer data enters, moves, and is stored? If no one can explain the data path clearly, controls are probably inconsistent.
- Are permissions role-based? Agents should only access the information needed for their queue and task.
- Are recording settings aligned to the type of interaction? Payment and sensitive-data workflows need extra scrutiny.
- Is access logged and reviewable? Leaders need proof, not assumptions.
Calling rules and consent management
- How is consent verified before outbound activity begins? A reliable answer should include system logic, not just agent instruction.
- How are opt-outs captured and enforced? If that process depends on manual memory, it will fail.
- Are scripts approved and version-controlled? Teams should know which script is current and who approved it.
- Can the operation show how disclosures work in both English and Spanish? Translation alone is not enough.
Training and quality assurance
- What does onboarding include for compliance-sensitive queues? Ask for examples of scenario-based training, not just policy acknowledgment.
- How often are agents coached on compliance findings? A mature program ties QA results to live coaching.
- Are bilingual calls reviewed by qualified reviewers? This matters more than many buyers realize.
- How are repeat issues handled? Strong teams fix root causes, not just individual errors.
Audit readiness and incident response
Use this quick screen when comparing providers or internal teams:
| Question | Good sign | Red flag |
|---|---|---|
| Is there a documented incident process? | Clear ownership and escalation | “We handle issues as they come up” |
| Are policy updates controlled? | Versioning and approvals | Informal script changes |
| Can managers produce evidence? | Call records, QA notes, access logs | Verbal reassurance only |
Vendor due diligence
If you are outsourcing, also ask:
- Who owns compliance alignment between client policy and BPO execution?
- How are script changes communicated to agents?
- What happens when legal or operational guidance conflicts with customer pressure?
- How quickly can the provider update bilingual workflows across teams?
If the answers are vague, the risk is real.
Conclusion Partnering for Peace of Mind
Call center compliance is not a side project. It is part of service design, workforce management, quality assurance, and client trust.
The companies that handle it well do not chase perfect paperwork. They build repeatable control into scripts, systems, training, and monitoring. They review live performance, not assumptions. They take bilingual and cross-border risk seriously instead of treating it like a translation task.
That is what turns compliance from a fear-driven obligation into a durable operating advantage.
For organizations that need secure, bilingual support without losing visibility or control, a nearshore partner can strengthen the model when the program is designed correctly from the start.
🚀 Build a Stronger Compliance-Ready Support Operation
CallZent helps regulated teams scale bilingual nearshore support with structured QA, secure workflows, and operational discipline built for real-world compliance demands.
Talk to an ExpertIf you want a nearshore BPO partner that understands bilingual operations, structured QA, and practical compliance execution, explore CallZent and see how its service model fits regulated customer support and back-office workflows.


 Start with policies agents can use
Start with policies agents can use Data handling and system access
Data handling and system access







